Security features in RapidDeploy
There are many aspects to security in RapidDeploy. Here we bring them together in one page.
RapidDeploy Application Security
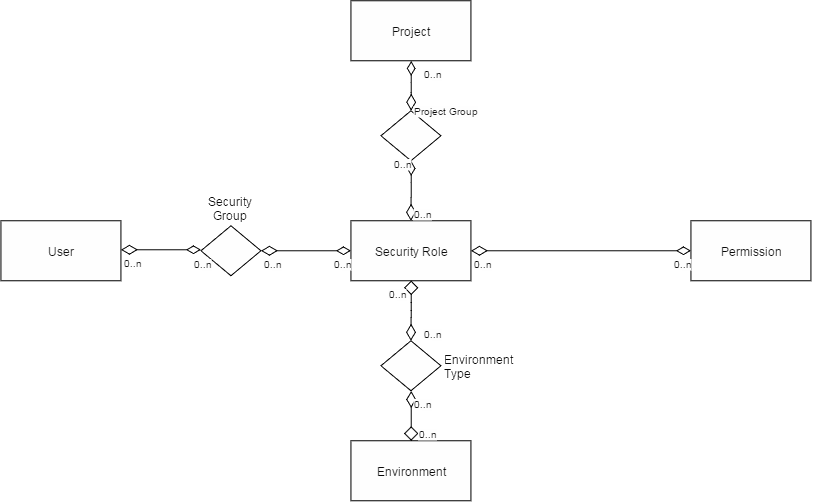
This diagram shows the relationship between Users, Projects and Environments.
1. Application Security in RapidDeploy
Application security concerns the constraints placed on the RapidDeploy user depending on the roles that they posess.
- Every action or feature in RapidDeploy has a Permission. Permissions are not user modifiable, but new permissions may be added in new releases of RapidDeploy.
- A Security Role is a collection of permissions.
- Standard roles are provided out of the box, but can be edited or added to by the customer.
- Roles may be GLOBAL or PROJECT scoped
- Roles are assigned to customer defined User (Security) Groups, Project Groups and Environment Types.
- Roles are additive and transitive (via groups)
- Users and/or Groups may be sourced from the RapidDeploy Database (default) or from the customers own LDAP Repository.
- Full details may be found in the documentation site.
2. Approval Groups
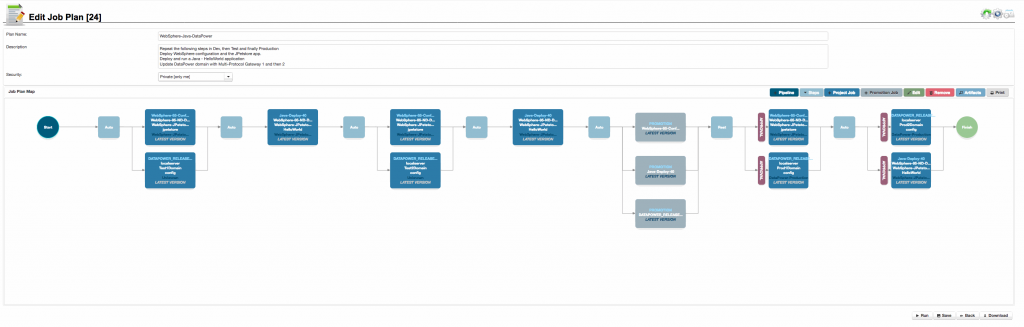
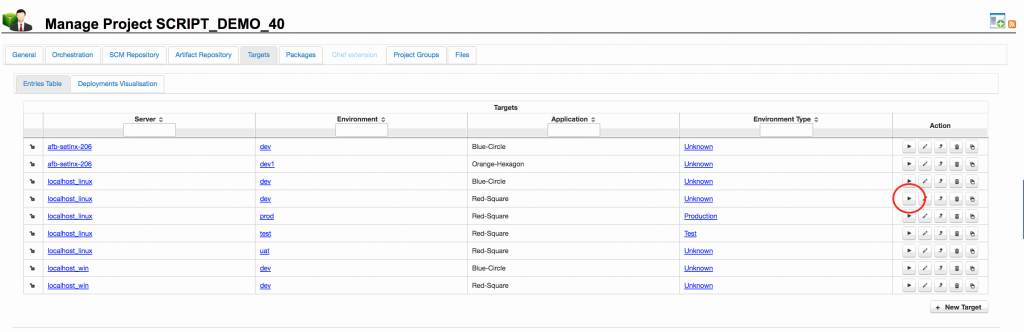
In order to configure the approvals process in RapidDeploy, you create an ‘Environment Type’ and associate it with one or more ‘Environments’. Further associating this ‘Environment Type’ with one or more ‘Security Groups’, results in any deployment to the target environment requiring an approval. A red approval gate appears in front of any such environment in the release pipeline, as shown in the screenshot to the right.
At least one user from each associated security group must approve the deployment, before it is allowed to proceed.
3. Single Sign-On (SSO)
- Single sign-on security providers are supported within the RapidDeploy Framework Application
- Pluggable SSO implementations
4. Property, Web Service Security and Late Property Injection
- All property fields in RapidDeploy may be set to encrypted and/or password protected. Encrypted fields are stored on the file system in an encrypted format. Password fields are not displayed in the GUI.
- Web Service Authentication Encrypter tool allows the user to create a token to pass in the header of all web service calls to RapidDeploy Web Services interface.
- Property Encrypter tool allows the user to encrypt values via the command line as the framework does it internally.
- ‘Late property Injection’. At job run selection time, any unset dictionary items for the target environment (not set at either project or target scope) will be presented to the user for completion. These may be left blank or filled in. These properties are only held in memory and not written to any file. This is useful where sensitive passwords cannot be stored, even in an encrypted format, in any file. In the screenshot to the right, the red ‘Empty’ field will be used for late property injection.
5. Remoting Security
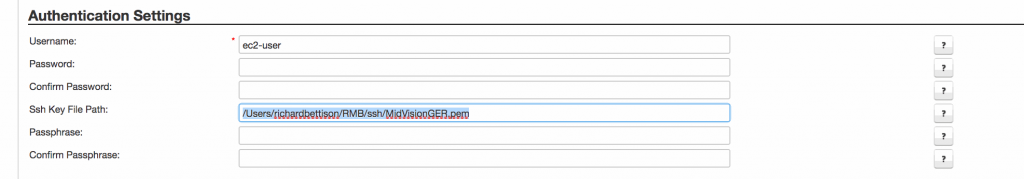
- Remote communication via SSH/SCP supports the standard security mechanisms:
- Username and password;
- Username and passphrase-less key;
- Username and passphrase protected key
- Key file
- Remote agent supports the following security between framework server and agent or agent to agent:
- SSL or Non-SSL socket connection;
- Automatic generation and propagation of SSL certificates if required;
- Multiple username and optionally encrypted password authentication
- Source host checking (only allow connections from trusted hosts)